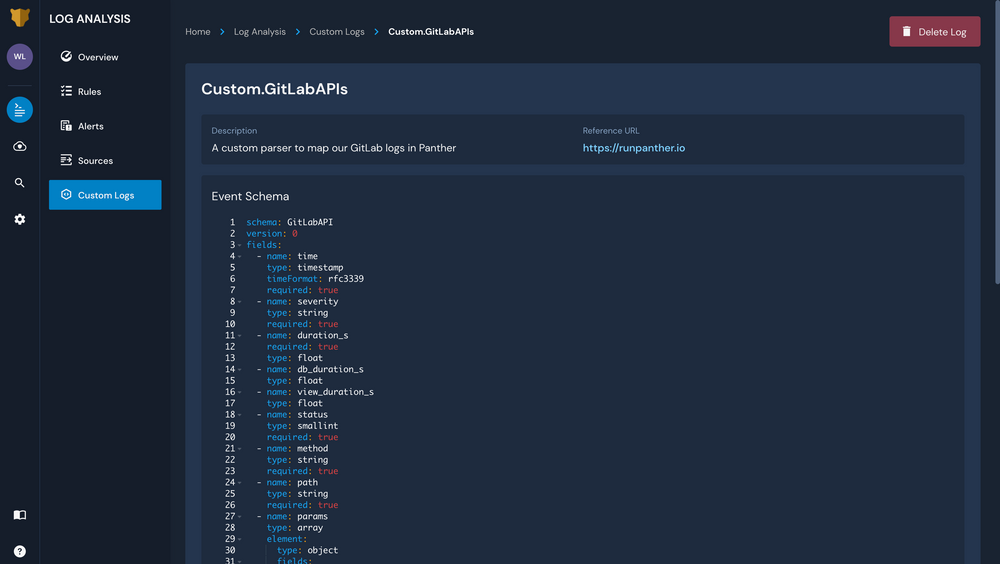
To quickly help you build a robust and scalable security data pipeline, Panther ships with pre-built log parsers for several high-value data sources like G Suite, Crowdstrike, Okta, Osquery, and more. With the new Custom Log Parsers feature in Panther Enterprise, you can onboard even more critical security data by defining YAML schemas to transform your raw logs into structured JSON data with extracted indicators for fields like IP Addresses and Domain Names.
The number of systems that security teams need visibility into is proliferating rapidly. By offering a fast and easy way to onboard custom data sources, Panther Enterprise helps security teams turn raw and unstructured logs into real-time alerts that provide actionable security insights. With clean log data from across cloud and on-premise environments, security teams can detect threats faster, correlate suspicious activity across systems, and investigate security incidents at scale to identify and remediate root cause vulnerabilities.
Custom Parsers can be written for any application that produces JSON, text, or CSV logs. Once your parser is defined and added to your instance of Panther, send your log data to AWS S3 and onboard the bucket as a data source in Panther to begin utilizing this data to power detection and response.
With Custom Log Parsers in Panther, you can bootstrap your security data lake with large quantities of structured log data from across your internal environment. Use this data to improve security posture, achieve complete visibility into systems and activity, and remediate vulnerabilities before they escalate into costly breaches.
Onboard even more critical security data to achieve complete visibility into systems and activity with Custom Log Parsers in Panther Enterprise.
