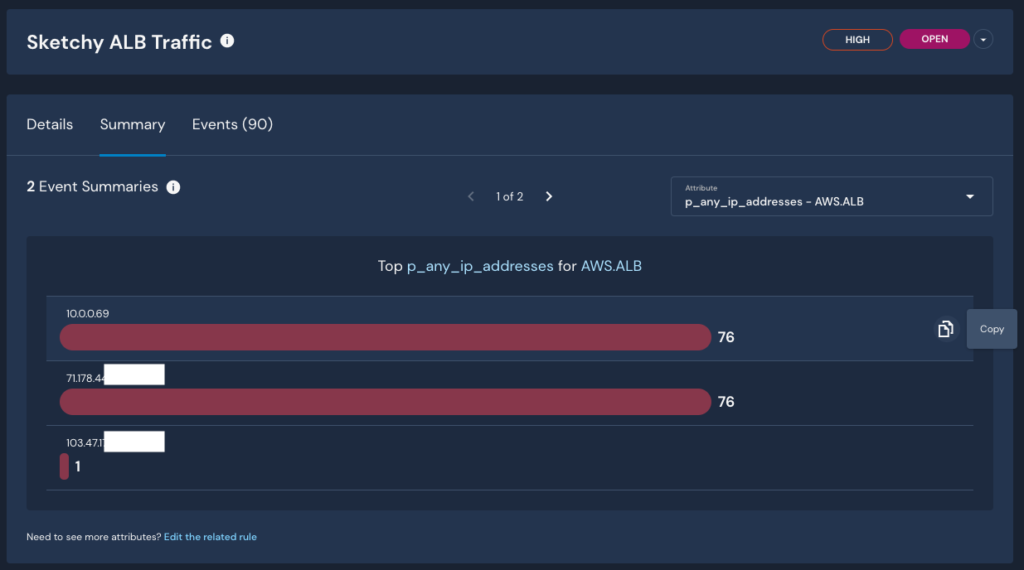
Alert Summaries are now available in Panther Enterprise! This feature is designed to speed up alert triage by proactively answering questions such as, “which unique IPs caused this suspicious behavior”?
Summaries help analysts quickly understand attacker patterns, correlate IOCs, and kickstart investigations.
To help reduce alert fatigue, Panther enables teams to group many events into one alert over a window of time (generally, 1 hour). By providing a proactive summary of these events, which could be in the hundreds, Alert Summaries help you quickly understand the context and severity of an alert.
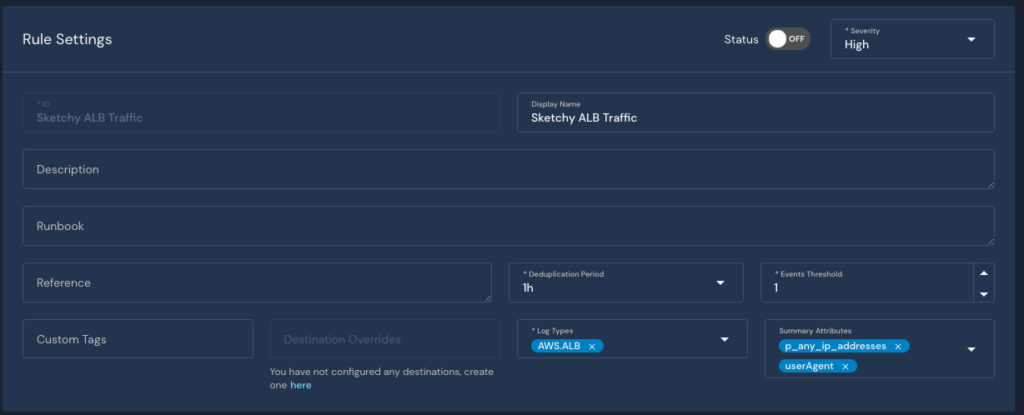
When creating a rule in Panther, you can declare which top-level attribute(s) are summarized in the associated alerts. These attributes can be adjusted as needed, and your Alert Summary table will update dynamically to show you the top five matches for the specific attribute(s) across events.
For example, say you have a rule to find “Sneaky” traffic hitting your load balancer. You can set your Summary Attributes to use the Panther standard field, p_any_ip_addresses, and the log-specific field, userAgent, and in your Alert Summary, you’ll see the top five values for each of those fields across all of your events (as shown above).
Swift analysis is critical for remediating threats before they escalate. Evaluating dozens or hundreds of events to correlate indicators is slow and inefficient. With Alert Summaries, you can quickly filter event data to achieve actionable insights that help you and your team determine how to respond to alerts.
With Panther’s Alert Summaries, you can:
Analyze alerts faster with dynamic summaries of data found throughout many alert-generating events.
