Resource Hub
Featured Resources
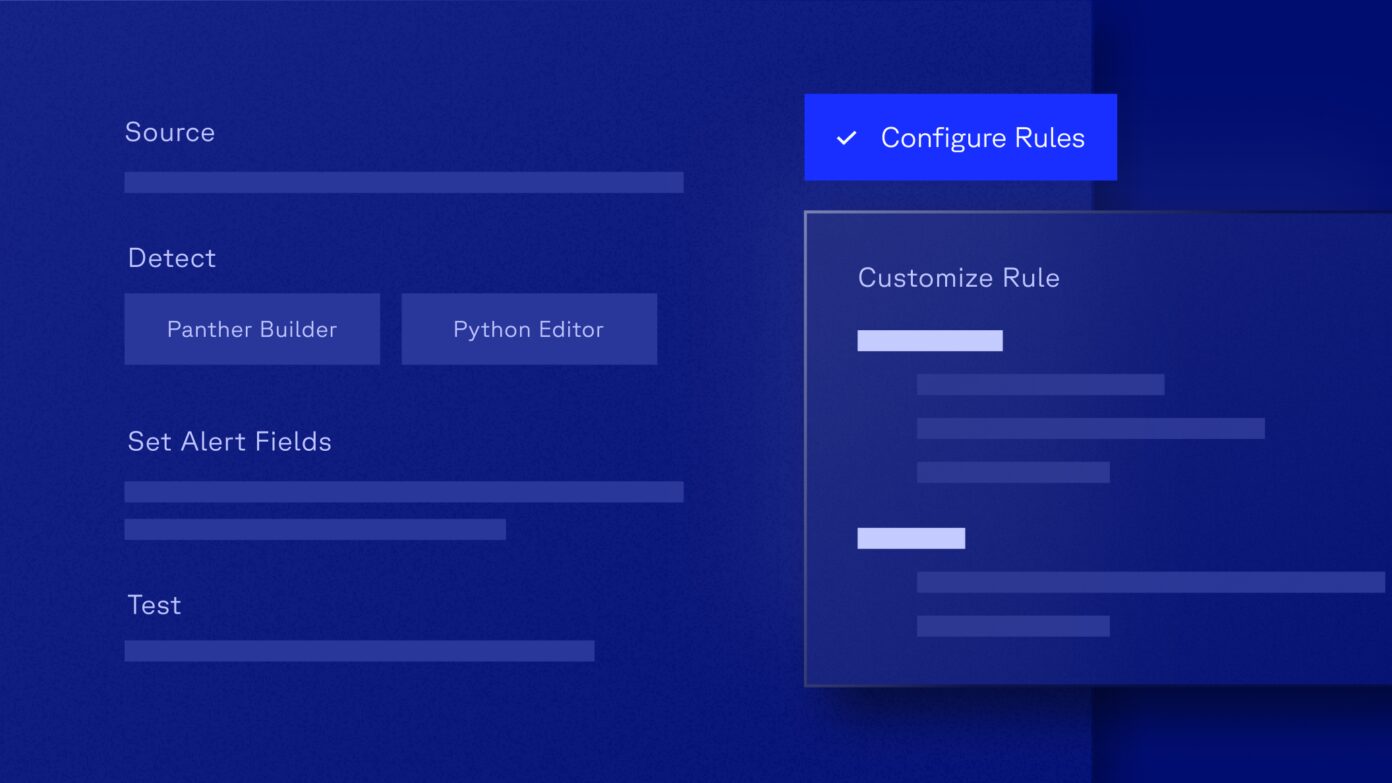
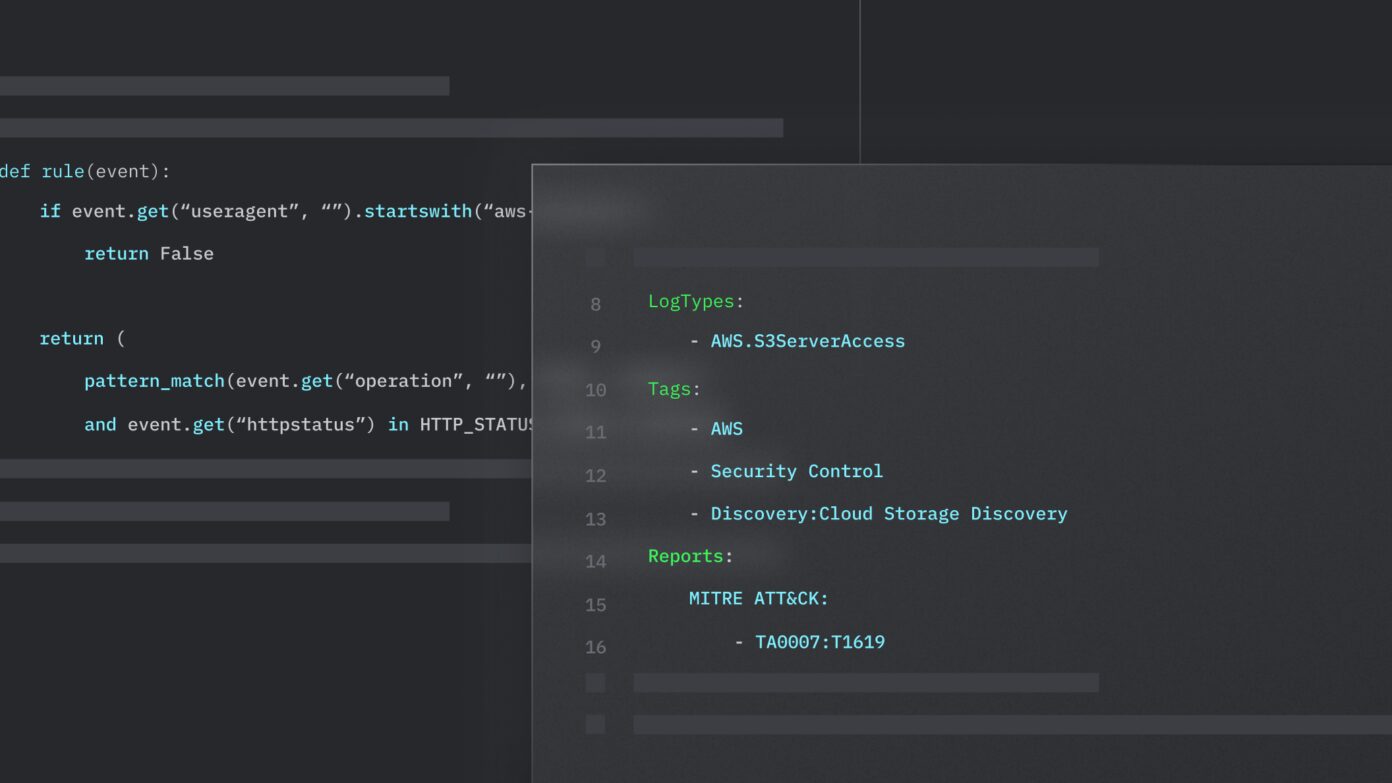
Detection-as-Code
All Resources
Blog
Why You Should Be Ingesting AWS CloudTrail Logs

Case Study
Benchling’s Code Driven Security Operations Program is Enabled by Panther
Blog
What You Need to Know About the Latest GitLab Vulnerability (Including Detection)
Podcast
SAP’s Matthew Valites on Why He Is a Proponent of Detection-as-Code

Blog
Is Your SIEM a Hotel California?

Blog
Unraveling SIEM Correlation Techniques
Blog
CVE-2024-3094 – Linux Supply Chain Compromise Affecting XZ Utils Data Compression Library
Blog
Critical Steps To Detect and Prevent Cryptojacking In Your Cloud Infrastructure